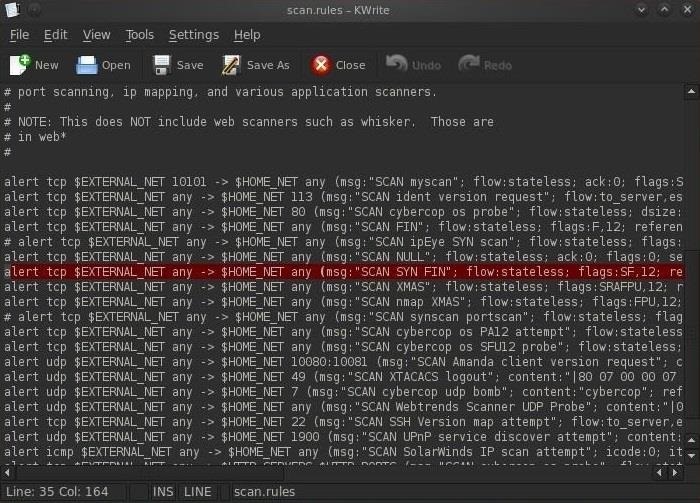
Figure 6 from Rule-Based Network Intrusion Detection System for Port Scanning with Efficient Port Scan Detection Rules Using Snort | Semantic Scholar
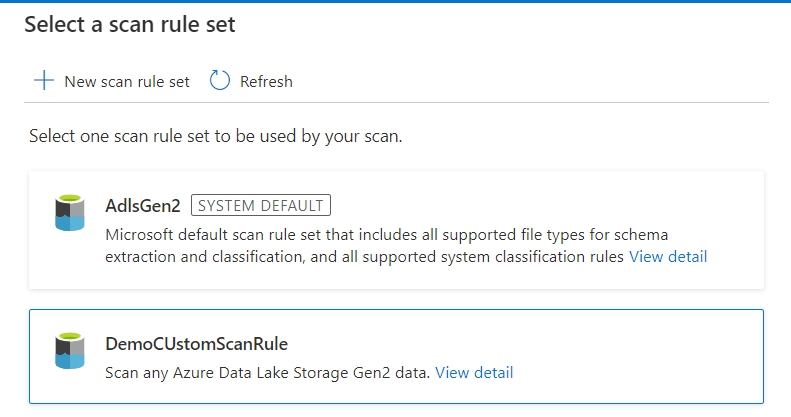
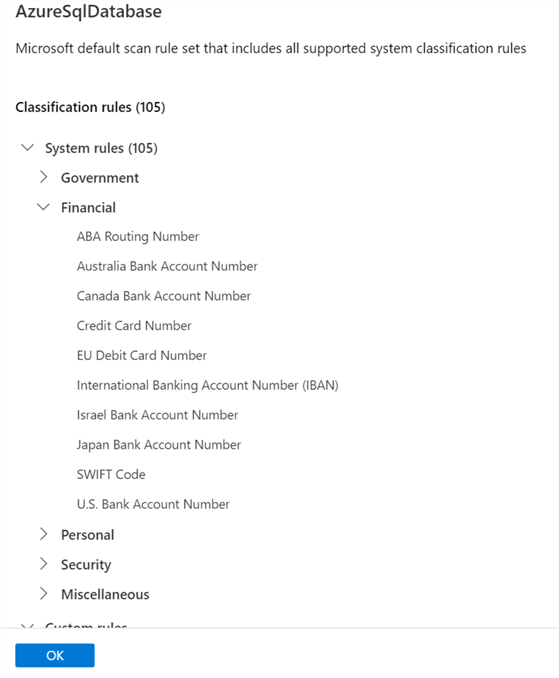
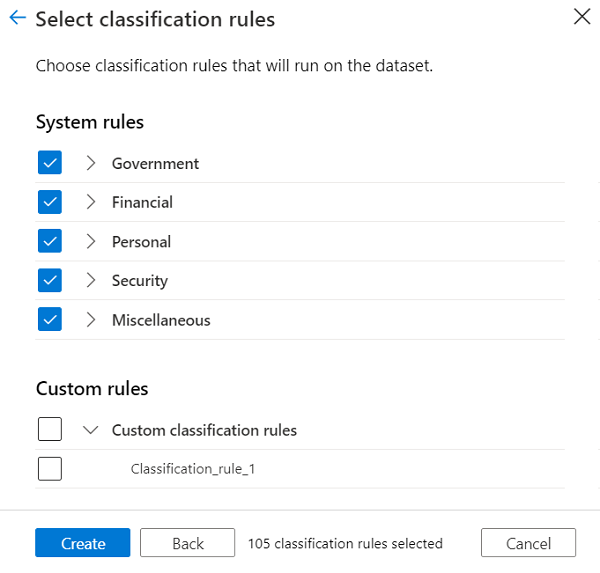
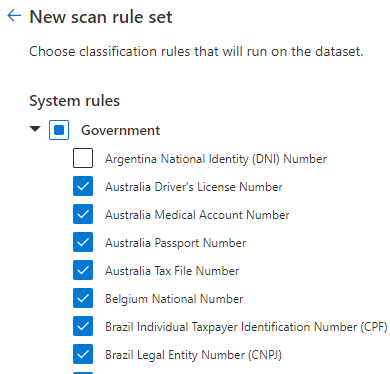
Quick overview of Purview. Recently I have been looking into… | by Subhasree Mohapatra | Jan, 2024 | Medium